Payments are about to change forever
Today, $24 trillion in digital payments flow through global infrastructure every year. Every one of those transactions is initiated, reviewed, and approved by a human being — a person tapping a card, clicking a button, authorising a wire. The entire payments stack, from authentication to compliance to audit, is built around the assumption that a person is on the other end.
That assumption is about to break.
The shift is not theoretical. AI agents are already initiating API calls, triggering payments, running sanctions checks, and onboarding customers. The question is no longer whether agents will handle financial transactions. The question is whether your infrastructure is ready to verify, audit, and trust them when they do.
Human payments vs agent payments: a fundamentally different trust model
Forty years of payments infrastructure has been built around a simple contract: a known human authenticates, authorises a transaction, and bears legal responsibility for the outcome. Every compliance framework — from KYC to PCI DSS to SOC 2 — assumes human accountability at the point of action.
AI agents break every one of those assumptions.
| Dimension | Human Payments | Agent Payments |
|---|---|---|
| Identity | Passport, driving licence, biometrics | No physical identity. No biometrics. No face. |
| Authentication | Password, 2FA, device fingerprint | API key? Certificate? Nothing standardised. |
| Authorisation | User clicks “Pay” — explicit consent | Agent acts autonomously. No click. No screen. |
| Audit trail | IP address, device, session, signed receipt | Which agent? Which version? Who deployed it? Prove it. |
| Accountability | Legal person bears liability | Agent has no legal personhood. Who is liable? |
| Compliance | KYC/AML built for humans | No KYA (Know Your Agent) standard exists today. |
| Risk | Fraud rate ~0.1% — decades of tooling | No historical data. No fraud models. No benchmarks. |
Every payment platform will face this gap. The platforms that solve it first will capture the agentic economy. The ones that don't will be left explaining to auditors why autonomous software made unsupervised financial decisions with no cryptographic proof of identity.
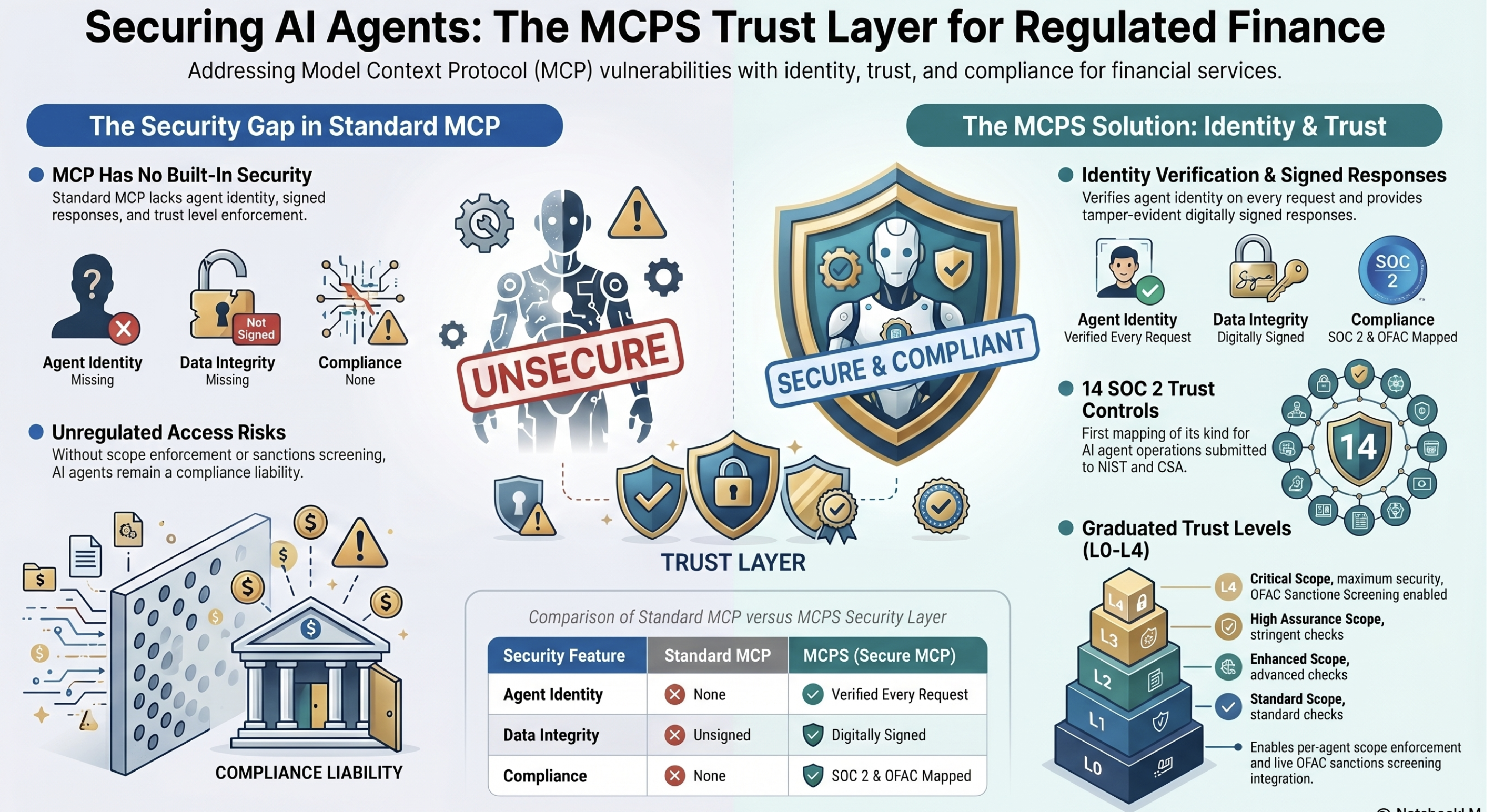
MCP: the universal connector — with no locks on the doors
In November 2024, Anthropic released the Model Context Protocol (MCP) — an open standard that lets AI agents connect to external tools, databases, and APIs. Within months, MCP became the de facto standard for agent-to-service communication, adopted by Claude, Cursor, Windsurf, and thousands of enterprise applications.
MCP solved the connectivity problem brilliantly. But it shipped with no security layer. No message signing. No agent identity. No replay protection. No integrity verification.
The result was predictable.
Tool poisoning. Prompt injection through tool descriptions. Remote code execution. Unrestricted memory allocation. Path traversal. These are not edge cases — they are structural consequences of deploying a protocol with no cryptographic security layer.
For regulated financial services, this is not a technical inconvenience. It is a compliance failure waiting to happen.
MCPS: the HTTPS of the agent era
CyberSecAI identified this gap in early 2025 — before the first MCP CVE was even filed. The response was MCPS (MCP Secure): a cryptographic security layer that sits on top of MCP without modifying the core protocol.
MCPS adds four primitives to every MCP interaction:
1. Agent Passports
Every agent carries a verifiable certificate proving who it is, who deployed it, and what it is authorised to do. No more shared API keys.
2. Signed Message Envelopes
Every MCP request and response is digitally signed. Messages cannot be altered in transit. The sender cannot deny having sent it.
3. Tool Definition Signatures
Every tool definition is signed before execution. Detects tool poisoning and definition tampering — the most common MCP attack vector.
4. Replay Protection
Every request carries a unique nonce and timestamp. Captured requests cannot be re-sent. Prevents replay and downgrade attacks.
MCPS is fully backward-compatible. Existing MCP clients and servers continue to function normally. MCPS-aware endpoints progressively negotiate security capabilities through five trust levels (L0–L4), from no verification through to full mutual authentication with revocation checking.
MCPS was submitted to the IETF as Internet-Draft draft-sharif-mcps-secure-mcp. It has since been cited as a formal defense mechanism in peer-reviewed academic research (arXiv:2604.05969), listed alongside security frameworks from Anthropic, Google, Microsoft, and NIST.
AgentPass: the security and trust layer for the agentic economy
MCPS secures the message. AgentPass secures the agent.
AgentPass is a complete agent security platform that delivers everything a financial institution needs to verify, score, monitor, and audit AI agents operating in their infrastructure. Think of it as the credit bureau for AI agents — the system that answers the question every payment platform must ask before processing an agent transaction:
What AgentPass delivers
| Capability | What it does | Why it matters |
|---|---|---|
| Cryptographic Identity | X.509 agent certificates with custom OIDs for scope, trust level, and deployer | Every agent proves identity cryptographically — no shared API keys |
| Trust Scoring | 5-dimension behavioural score (0–100) that evolves with agent actions | Agents earn authority through proven behaviour, not static permissions |
| Sanctions Screening | 75,784 entries (UK HMT + US OFAC SDN) screened on every transaction | AML compliance built into the agent layer, not bolted on afterwards |
| Spend Controls | Per-transaction and daily limits enforced by trust level | Rogue agents cannot exceed their authority — limits are cryptographically enforced |
| Anomaly Detection | Magnitude, velocity, recipient, and timing anomalies detected in real time | Trust automatically adjusts when agent behaviour deviates from baseline |
| Audit Trail | Hash-chained, tamper-evident logs in JSON and RFC 5424 syslog format | Every agent action is non-repudiable and SIEM-ready from day one |
| MCPS Signing | Ed25519/ECDSA P-256 per-message signing on all MCP responses | Message integrity and origin verification on every API call |
Three lines of code. Not three months of architecture.
AgentPass was designed for platform engineers who need to ship, not for consultants who need to consult. Integration is measured in hours, not quarters.
Open Source SDKs
agentpass-go and mcps-go are Apache 2.0 licensed. Free to use, free to modify, free to deploy. No vendor lock-in. No license fees on the SDK layer.
Middleware Pattern
AgentPass integrates as HTTP middleware. Wrap your existing MCP endpoints. Agent verification, sanctions screening, and MCPS signing happen transparently before your handler is called.
Already in Production
AgentPass and MCPS are merged into the master branch of moov-io/watchman, an open-source sanctions screening platform used by financial institutions. Not a proof of concept — production code, reviewed, tested, and merged.
Self-Hosted
AgentPass Self-Hosted ships as a Docker container with built-in CA, PKI, dashboard, sanctions screening, and audit logging. Deploy in your own infrastructure. Your keys never leave your network.
No one else is doing this
The market for agent-to-service security in financial services is wide open. Existing approaches fall short in fundamental ways:
API Keys
Static secrets with no identity binding. Cannot distinguish between agents. Cannot prove which agent made which call. Cannot revoke without rotating the entire key.
OAuth / JWT
Designed for human users authenticating via browsers. No concept of agent trust levels, behavioural scoring, or autonomous transaction limits.
Payment Rail Protocols
Visa TAP, Mastercard Agent Pay, and Google AP2 define how agents interact with payment networks, but do not address who the agent is or whether it should be trusted.
KYA Providers
Emerging Know-Your-Agent solutions focus on identity registration but lack runtime trust scoring, cryptographic message signing, and compliance mapping.
AgentPass is the only solution that combines cryptographic agent identity, behavioural trust scoring, per-message signing, sanctions screening, anomaly detection, and SOC 2 control mapping in a single, deployable platform. It is the layer that sits between the agent and the payment rail — verifying identity, scoring trust, screening sanctions, and proving every action to auditors.
Your auditor will ask these questions. We built the answers.
When AI agents begin making financial transactions in your infrastructure, every compliance framework you operate under will need answers to questions that did not exist twelve months ago. AgentPass provides them out of the box.
SOC 2 Control Mapping
14 Trust Service Criteria mapped to AI agent operations. CC6.1–CC6.8, CC7.1–CC7.4, CC8.1, A1.1, PI1.3. Submitted to AICPA, CSA, ISACA, and NIST.
PCI DSS v4.0.1
Complete compliance mapping submitted to PCI SSC. Agent operations mapped to cardholder data environment controls.
EBA / PSD2
Position paper on AI agent payments submitted to the European Banking Authority. Strong Customer Authentication implications addressed.
FCA Regulatory Sandbox
Application submitted for autonomous agent payment oversight. Regulatory engagement in progress.
OWASP MCP Security
Contributor to the OWASP MCP Security Cheat Sheet (Section 7: Message Integrity). OWASP MCP Top 10 contributor.
IETF Internet-Drafts
10 Internet-Drafts submitted, including MCPS, AgentPass Payment Trust, ATTP, and AEBA. Standards-track submissions.
These are not aspirational roadmap items. Every submission has been filed, every mapping has been completed, and every framework alignment has been documented. When your auditor asks, you point to the evidence.
Built by people who have been securing critical infrastructure for three decades
Raza Sharif
Raza Sharif brings over 30 years of experience in cybersecurity, having served as a trusted advisor and architecture delivery lead for international governments, financial institutions, and private sector organisations across EMEA and North America.
Fellow of the British Computer Society (FBCS), CISSP, and CSSLP certified. Published author of “Breach 20/20” on data breach prevention. UK Government Security Cleared (SC). OWASP contributor. Discoverer of multiple CVEs across the MCP ecosystem. Author of the MCPS IETF Internet-Draft. Cited in peer-reviewed academic research alongside Anthropic, Google, Microsoft, and NIST.
CyberSecAI Ltd (Company No. 16837162) is a UK-registered cybersecurity company headquartered at 205 Regent Street, London. The company is focused exclusively on securing the agentic economy — the infrastructure that will process trillions of dollars in AI-initiated transactions over the coming decade.
The window is now
McKinsey projects $5 trillion in agentic commerce by 2030. Gartner predicts 20% of transactions will be programmable for AI agents. The MCP ecosystem has already seen 30+ CVEs in its first 60 days — 6 discovered by CyberSecAI. Regulators are watching. Auditors are preparing questions. Your competitors are evaluating.
AgentPass is the only platform that provides cryptographic agent identity, behavioural trust scoring, sanctions screening, per-message signing, anomaly detection, and SOC 2 control mapping in a single deployable solution — already integrated into production financial infrastructure.
The agents are coming. The question is whether they arrive at your platform verified, scored, and auditable — or anonymous, unmonitored, and indefensible.
Enable secure agent payments
Talk to CyberSecAI about integrating AgentPass into your payment platform.
Contact us →